Have you ever seen an email that contains a fake invoice with a link or an email from Facebook asking you to reset your password that doesn’t look quite right? Chances are, it’s a phishing attack. Let’s explore what phishing attacks are and what you can do to prevent and protect yourself against them.
What are phishing attacks?
Phishing attacks are a type of cyber-attack that involves tricking someone into giving up sensitive information, such as login credentials, personal or financial information. Attackers will often use spoofed emails or websites that look legitimate to steal this information. Many types of phishing attacks use a wide range of attack vectors. Such as Email, SMS and websites. Here are three examples that are very relevant to businesses of all sizes.
Spear phishing: This type of phishing attack is targeted at a specific individual or organisation. The attacker will often create a fake email or website that appears to be from a trusted source, with the aim of tricking the victim into entering sensitive information such as credentials.
Whaling: Is a highly targeted attack. Targeting high-profile executives with access to highly valuable information. This will also often be in the form of fake emails, SMS and webpages.
Clone phishing: A clone phishing attack is a highly sophisticated attack where the hacker will create an identical copy of a message or email that the target has already received. They often send it with a context such as “resending this”. The content will then include a malicious link.
How to defend against Phishing Attacks
To best defend yourself from phishing attacks, education on the methods and systems that are used in attacks is important. Being cautious when giving out personal information online is a must. If you receive an email or are directed to a website that looks suspicious, do not enter any sensitive information. You can also use anti-phishing software to help protect yourself from phishing attacks.
In summary, some things you can do to avoid these attacks are:
- Be aware of the different types of phishing attacks. This will help you to be more suspicious of emails or websites that may be fake.
- Do not click on links in emails from people you do not know. If you are unsure about the legitimacy of an email, contact the person who supposedly sent it to verify that it is real.
- Do not enter any sensitive information on websites unless you are absolutely sure that the site is legitimate. If you are unsure, contact the company directly to ask if the site is real.
- Install anti-phishing software on your computer. This software can help protect you by blocking phishing websites
- Employ good email filtering and boundary protection on your devices. This will significantly reduce, if not remove, the chance of an attack reaching you at all.
The scary truth of phishing attacks
Tech-savvy people among us may think they are under no threat, but unfortunately, this is far from the truth! In 2021, Phishing was involved in 36% of all large business data breaches. Human Intelligence is the best defence against phishing attacks. They can be so convincing and sometimes indistinguishable from an email sent by a colleague or client. Just because you’re aware of one of the types of phishing attacks does not mean you aren’t vulnerable to another.
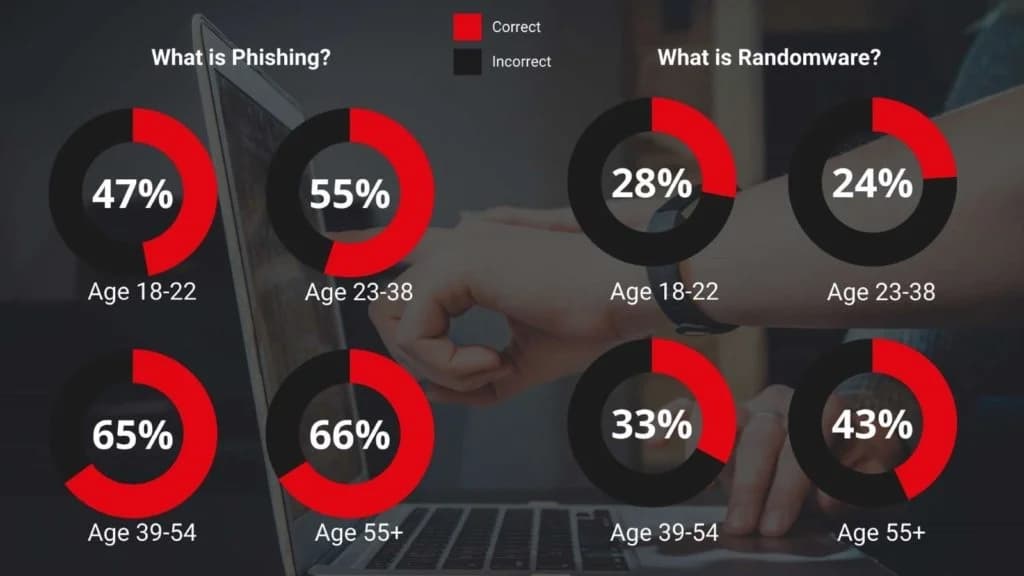
Proofpoint ran an experiment in 2022 that took an in-depth look at user awareness, vulnerability and resilience to a phishing attack. In their survey of over 3,500 adults, 600 of them were IT Security Professionals. Here are the results of some fundamental questions. If you’re interested in expanding your knowledge about phishing attacks, see our: Phishing Attack Trends 2022
Where ITC Service can help
ITC Service was built from the ground up with Cyber Security in mind. Our suite of tools will make you resilient to all types of cyber-attacks. Everything from endpoint protection and network security to assisting your business in passing Cyber Essentials, we can do it all. Visit our Cyber Security page to find out a little more, or get in touch today for a free, no obligations consultation.









